Half a World Away
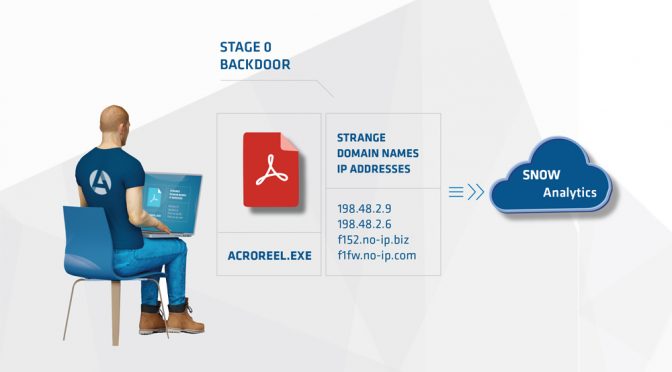
1) A new Arc4dia client had been hacked twice in the past (before Arc4dia), each time during an important international contract negotiation.
2) After each hack, the implant found had been removed from the infected machines and the admin account used had its password changed.
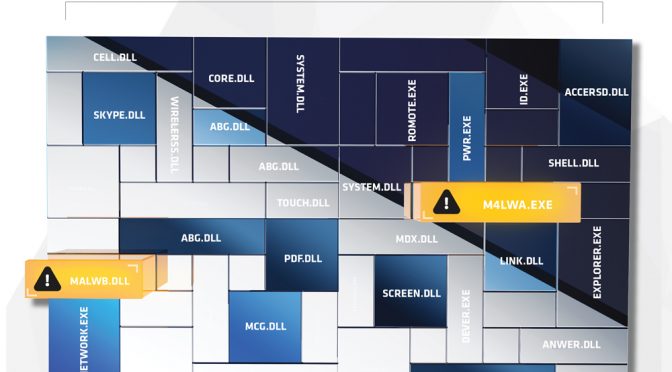
3) For a third time, now with Arc4dia present, they got hacked. A service started appearing on several machines.
4) While Arc4dia tracked hosts being infected and disabled the implants, we discussed having the client’s system administrator’s track down the origin of the credentials being used.
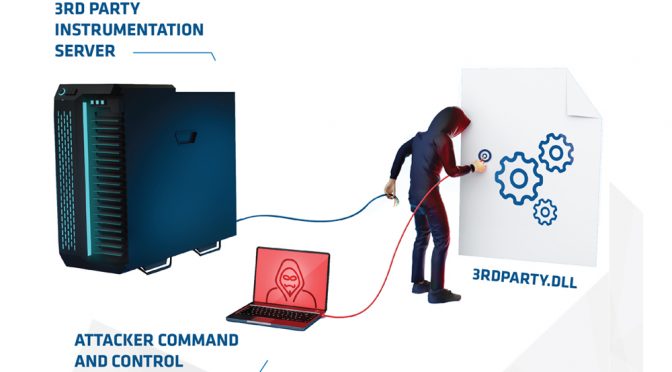
5) Through our investigation, it became clear that the attacker was coming in from inside the network, but also from a rogue device located at a field oce in Asia. When local employees working out of this oce were contacted, they denied the presence of a rogue device.
6) When local employees working out of this oce were contacted, they denied the presence of a rogue device.
7) Arc4dia, having extremely varied and specialized resources was able to provide assistance to the client since the investigation was not firmly rooted in the Human Intelligence side of things.
8) With the client, Arc4dia formulated a plan to provide experienced personnel to go to the remote oce, posing as international employees in order to investigate the nature and origin of the device.
9) A wireless router providing remote VPN access was identified and Arc4dia was able to provide Subject Matter Experts for the client’s legal case against the employee in question.
Sometimes employees can be a client’s main security problem. Arc4dia can help identify them.